
You must be receiving security patches from Google or your phone’s OEM via OTA updates on your device. Do you know what Android Security patches are, what do they mean and why are they important? In this article, we’ll take a detailed look at the Android security patches and explain what they have to offer.
Android has been focusing on security since day one. It is built on top of the Linux kernel and makes use of several of its strong security mechanisms. The whole operating system framework is developed following strict rules. These make it possible to provide full isolation between the operating system kernel, system processes and libraries, and Java Apps. Every new Android version uses a kernel in sync with the official (upstream) Linux kernel and defects found in the framework in previous releases are addressed by Google engineers.
Early in Android’s development process, it became apparent that security enhancements were usually coming late. During the annual release cycle of the Operating System, a big number of security defects were found. However, no fix would come until the next Android release. Most of the time, fixes were only made available on the next Android version and devices should be upgraded to be safe. Even if fixes were also applied to earlier versions of the Operating System, most manufacturers would not create Over The Air (OTA) updates for non-flagship devices to provide these fixes: The cost of such a task was just very high.
Google tried to come up with a solution to this issue: Since 2015, Google has been releasing monthly security bulletins. These include information about newly found security defects and links to the patches that address them (known in the community as security patches). Although Google usually splits these patches into several groups in their bulletins, they can be generally categorized as kernel patches – targeting the kernel versions currently officially supported by Android – and system patches – which fix issues affecting the rest of the Android stack. Patches for security defects are available around one month after the vulnerability is exposed, with the next bulletin.
What does Android Security Patch mean?
Google’s security patches cover Remote Code Execution, Elevation of Privilege, Information Disclosure and Denial of Service vulnerabilities. These types of vulnerabilities allow a possible attacker to gain special access on a device without the user’s input. For example, a malware app would need to be installed first and then opened by the victim in order to steal information or charge the user’s account. Do not forget to read my exhaustive article about malware on Android. On the other hand, an attack through Remote Code Execution could happen without the user even noticing it. Users are not able to do anything to protect their devices from the types of security vulnerabilities discussed above, except running an Android version with the latest security patches.
In general, running an Android with the latest security patches provides protection from attacks that can steal personal information (including passwords, bank accounts data and phone numbers), cause damage to the software of a device, and spy on the victim (through location tracking, voice recording, etc).
The Status of Security Patch support
One could find the above security vulnerability management very interesting. However, while the code available on Google’s code repositories is constantly updated with the latest security patches, it is still up to the manufacturer to implement these on their current (through OTA Updates) and future devices. This is considered difficult to achieve because most manufacturers do not have the human resources needed to complete this task. Moreover, versions of Android shipped with most devices are heavily customized by the manufacturer to add special features. Applying Google’s patches on top of these special Android builds might require extra modifications to the code.
Apart from the above, some security vulnerabilities affect proprietary code traditionally released by the System-On-Chip (SoC) distributors (eg Qualcomm, MediaTek). Only they would be able to fix these issues. Most of the time, these issues remain unaddressed on older hardware.
It becomes clear that, while Google does its best to provide easy solutions to most of the security vulnerabilities of its Operating System, the huge number of devices running Android and its great variation in hardware characteristics make it difficult to apply security fixes to all of them.
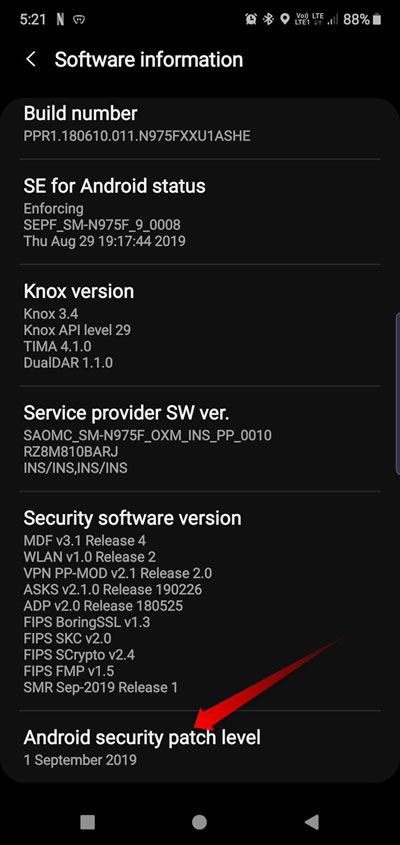
Find the Security Patch version you are running on
You can find what version of security patches your Android (6.x +) is patched with, by going to Settings and then About Phone. There, you should find a Text-view named Android security patch level. Google provides two types of security patch levels each month. One, on the first day of the month (e.g. September 1) and the other one on the fifth (e.g. September 5). The patch level of the first day of the month covers security issues addressed in that month’s bulletin, while the patch level of the fifth day covers all security issues addressed so far.
If you feel that your phone is lagging or running slow, you must read our tips to speed up lagging Android devices. Moreover, these Android RAM management tips would also help you tweak your phone for the best possible performance.
How to get the latest Security Patches
Unless you are a developer yourself, you have to rely on other developers or manufacturers to get security patches. Most manufacturers usually have a common code repository for each Android version, for all their supported devices. This means that budget and high-end devices could share code. In the end, though, only high-end devices will get any security patches due to reasons discussed before. So, if you want to always run the latest security patch level, you can either buy a high-end device from a manufacturer known to provide OTA updates often or buy any device that has a custom ROM available for active development. Most big names in the custom ROM space, like LineageOS and OmniRom, tend to apply security patches some days after their release by Google.
You should also keep in mind that, kernel patches are applied to devices differently on custom ROMs. Usually, each device (or devices running on the same SoC) has its own kernel code. It is the device maintainer’s responsibility to apply the kernel patches. While you can rest assured you will get the latest patches on the next update, your kernel might still be exposed to risk if it is not under active development. Most custom ROMs have strict rules for this scenario. A device that sports an unmaintained kernel for quite long is removed from the ‘official devices’ list.
Conclusion
To sum everything up, there are two ways to always run the latest Security Patches on your device:
- Get a high-end device from a manufacturer that has established a good name on OTA updates
- Get a device with custom ROM support, which also enjoys a big community of users and developers.
The second solution seems the best since most custom ROM distributions provide monthly updates. This is more often than most manufacturers on stock ROMs.
That is all you should know about Android’s Security Patches. If your current device is not capable of getting the latest Security Patches, you should definitely have Security Patches support in mind when buying your next device.
Read Next: All You Need to Know About Android System WebView



Join The Discussion: